Research Security and Export Control
In light of the changing geopolitical situation, international knowledge and technology transfer is increasingly subject to legal and security-related requirements. Export control encompasses all legal requirements governing the transfer of certain goods, technologies, software, or information. Knowledge and research security goes beyond this and aims to protect research, knowledge, and institutions from security-related risks. Both areas overlap, particularly in the context of international cooperation and sensitive technologies.
As part of its internationalisation strategy, the University of Greifswald is strengthening the international orientation of its research and teaching. Compliance with export control regulations is mandatory. Relevant situations may include international research collaborations, business and research trips, the shipment of equipment, data, software, or samples, the development and transfer of technologies, and the employment of personnel (see case studies).
All researchers and employees are therefore required to consider aspects of knowledge security and export control at an early stage in order to avoid legal and security-related risks.
The university is committed to the goals of export control and promotes awareness of sensitive research and the responsible use of knowledge and technologies in order to strengthen the university's resilience in a growing geopolitical dynamic.

Research Security and Export Control
Dr. Jakob Krieger
phone: 03834 420 4254
forschungssicherheit
Information and consulting
eLearning offering:
Further information:
Science-related information from the Federal Office of Economics and Export Control (BAFA)
Position paper by the German Science and Humanities Council: “Science and security in times of global political upheaval”
Joint Committee on Security-Related Research (DFG and Leopoldina)
Country-specific information on research cooperation (DAAD)
Position paper by the Federal Ministry of Education and Research (BMFTR)
in German only:
Rechtsgrundlagen - Legal basis (BAFA)
FAQs - Frequently asked questions related to export control and research/knowledge security:
Universities, scientific institutions, and their employees are subject to the same foreign trade restrictions as all other persons and institutions when engaging in international exchange. This applies not only to activities requiring authorization, such as the export of goods, e.g., scientific samples, chemicals, or equipment as classic exports, but also to the transfer of knowledge, for example through email correspondence with foreign colleagues, through presentations at conferences abroad, or the transfer of knowledge and access to foreign visiting scientists (see p. 17 in the Export Control and Academia Handbook).
Security-related research affects all departments. It refers to scientific work where there is a risk that findings, technologies, or products could be misused—for example, to endanger human dignity, life, health, freedom, property, the environment, or social peace. Such research is considered particularly critical if misuse is immediately possible and could potentially cause significant damage. Security-related research also involves collaboration with individuals, organizations, and institutions that are listed on so-called sanctions lists or originate from countries subject to embargo regulations, regardless of the research topic.
Researchers and employees involved in research and teaching have a central responsibility to assess and classify their own work in accordance with export control regulations. The University of Greifswald supports you in this by providing advice, reviews, and organizational measures. If in doubt, please contact the export control officer—this can help to clarify uncertainties and avoid problems later on.
The permit requirements under foreign trade law essentially relate to the following activities:
Export and transfer of items
The terms “export” (Ausfuhr) and “transfer” (Verbringung) describe processes in which items (goods, software, or technology) are sent abroad. While the term ‘transfer’ refers to the delivery or transfer of items to another EU member state, the term ‘export’ refers to the delivery or transfer of items to a third country, i.e., a country outside the EU. Items subject to licensing requirements include, on the one hand, items specified in the item-lists (so-called listed items) and, on the other hand, unlisted items that are exported or transferred in connection with a critical use (catch-all clause).
Supply ban and technical support
A supply ban (Bereitstellungsverbot) refers to measures that are also known as sanctions or embargoes. It can be directed against individuals, organizations, institutions, or an entire country. In addition, various items, commodities, services, technical assistance (such as repairs), or financial transactions in general may be affected, or certain groups of items, such as weapons or military equipment, may be subject to a supply ban. A wide variety of combinations are possible. For example, a country may be subject to a general supply ban (total embargo), but humanitarian items and goods may be delivered/supplied, however, they require special permits from the Federal Office for Economic Affairs and Export Control (BAFA).
Technical support (Technische Unterstützung) refers to the transfer of intangible knowledge and skills (“knowledge in the head”); primarily, therefore, the verbal transfer of information, e.g., in seminars, workshops, research collaborations, or when working with foreign guest students and researchers.
This is to be distinguished from the export or transfer of technology, i.e., the cross-border transfer of embodied technology, for example, in the form of an email, a data carrier (storage media or end devices), or by making it available in a cloud to which persons from abroad can also gain access.
Trading and brokerage transactions
A trading or brokerage transaction may exist, for example, if a person contributes through a trading or brokerage activity to goods located in a third country being shipped to another third country.
Yes, compliance with export control laws is monitored by the Federal Office of Econom Affairs and Export Control, e.g., as part of foreign trade audits conducted by federal customs (Zoll) or the federal bank (Bundesbank). Export control laws are punishable by law, i.e., violations can be punished with heavy fines or imprisonment of up to 5 years, e.g., in the case of exports requiring permits without approval, or violations of EU embargoes or sanctions regulations.
Certain knowledge and certain items can potentially be used for military purposes or misused in a variety of ways—this is referred to as items of dual or multiple use. The decisive factor here is not the actual or general use, but solely the possibility that this knowledge or these items could be used or misused for military or security-threatening purposes. For this reason, export—i.e., transfer to certain countries or recipients—may be restricted or subject to authorization.
This applies not only to the physical export of devices or laboratory equipment, but also to the transfer of knowledge—for example, by email, (mobile) data storage devices, cloud systems, or in personal conversations, for example with visiting scientists.
As a rule, the transfer of knowledge that is already publicly available or of research that is considered basic research (from the perspective of foreign trade regulations, not necessarily from the perspective of the field) is not a cause for concern. These are often exempt from permitting requirements.
Researchers have a duty of care (due diligence) and must carefully check items and potential cooperation partners—whether individuals or institutions—in advance. This involves evaluating objectives, strategies, ethical standards, and potential risks. The aim is to make informed decisions for trusting, secure, and long-term sustainable collaborations. A structured due diligence process helps to identify risks at an early stage and avoid potential damage.
Export Control - Criteria for checking:
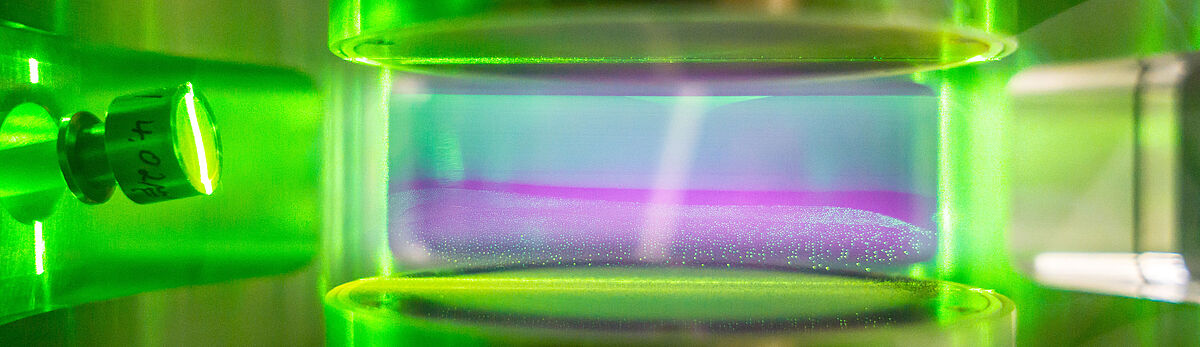
- A first indication of whether your own research could be subject to export control permitting requirements is to carefully review your own research work with regard to the lists of items (military equipment and dual-use goods). A connection to the items-lists exists regardless of whether the listed items are physically available for your own work and are only used methodologically (e.g., high-power lasers in imaging procedures) or whether research is being conducted on or with listed items (e.g., the development of high-power laser technology).
- Another indicator is references to embargoed countries. This applies to the employment of persons or exchanges or cooperation with persons from embargoed countries, as well as travel (research or conference trips) to these countries.
- The employment of or cooperation with individual persons or cooperation with certain organizations may also be subject to export control regulations, e.g., in the context of national or European sanctions. Therefore, when initiating a potential cooperation or business relationship, check whether your future cooperation or business partners are listed on national or European sanctions lists (a quick guide to checking sanctions lists for individuals or organizations can be found under “Further information and resources/Downloadable content”).
If you suspect that your research/activities may be subject to export control licensing requirements, after an initial self-assessment, you can obtain assistance with the assessment and a possible BAFA permit application from the export control officer.
Yes, export control regulations also apply to business trips, both for research stays and for attending conferences or lecture tours. Taking controlled items such as samples, data and software, chemicals, or prototypes to third countries constitutes an export requiring authorization (even if it is only temporary). Before any business trip abroad, please also refer to the information provided by the The German domestic intelligence services on “Business Travel Security” and the country-specific travel advice (in German only) provided by the Federal Foreign Office for your own safety.
The disclosure of already published findings is generally unproblematic and therefore does not require approval. It should be noted that even the first publicly accessible presentation of unpublished data with possible dual-use relevance to an international audience in the form of lectures or poster presentations can be considered knowledge export and thus constitute an export requiring approval under foreign trade law.
Lectures or presentations on technologies related to military equipment or unpublished dual-use technology should only be given for security-related assessment purposes after prior consultation with the export control officer. It is irrelevant whether publication is planned at a later date.
If a conference is taking place in or is being organized from an embargoed country, please contact the export control officer before registering.
The publication of scientific articles is one of the central tasks of science. Knowledge that has already been published is not subject to approval. Nevertheless, the publication of research results is also subject to legal requirements, compliance with which must be ensured by the university if there is a security-related connection (e.g., in the case of defense equipment or dual-use goods).
According to the standard practice of the Federal Office for Economic Affairs and Export Control, the first-time publication of previously unpublished data (e.g., manuscripts, preprints, lectures prior to approval) can be considered a controlled export. The exception for knowledge that is already publicly available does not apply in this case, as research results are only considered “generally accessible” once they have been published.
If you believe that this could be the first publication of research results that are potentially relevant to export controls, please contact the export control officer at an early stage.
Collaboration with international researchers and other organizations (companies/service providers) may be relevant under export control law if controlled items, software, or technologies (e.g., dual-use-items) are made available—regardless of whether this is done physically, digitally, or verbally. Activities in Germany can also be considered exports, for example, when collaborating with foreign guest researchers or in the case of sensitive end uses. The content of the research, access rights, and end use are decisive factors—not just the location.
In the case of international cooperation, other national export control regulations may apply in addition to German ones. An early check during the initial phase helps to avoid legal and security-related risks.
There are several exceptions to the licensing requirements relating to export controls. For example, licensing requirements do not generally apply to technologies derived from basic scientific research or to information that is already publicly available. Information required for patent applications is also exempt. In addition, there are export facilitations such as the so-called General (Export) Authorisations (GEAs or AGG - only available in German), which can be used in specific cases and thus replace an application for a license.
Technologies or software that are publicly available on their further distribution (copyright restrictions or paywalls do not prevent general accessibility in this sense) are generally accessible. These include, for example:
- Publications such as books, magazines, or newspapers in bookstores or public libraries
- Information that is freely accessible on the Internet (without registration)
- Freely accessible information from open conferences, seminars, trade fairs, or exhibitions (handouts, flyers, brochures, etc.)
- Information published by patent offices
- Basic scientific principles as commonly taught in schools and universities (textbook knowledge)
- Dissertations or theses, provided they are publicly accessible in accordance with the usual regulations
Basic scientific research encompasses experimental or theoretical work that primarily serves to gain knowledge about fundamental principles and is not geared toward a specific practical goal. This includes, for example:
- Research aimed at expanding fundamental scientific knowledge
- Investigations into fundamental solutions or procedural approaches
- Theoretical and experimental work without direct product development
However, work that is clearly aimed at developmental steps towards specific products or applications is no longer considered basic research.
In addition to the technology readiness level, the origin of the research funds or the type of cooperation partners (e.g., industrial cooperation) may also be relevant for classification. However, a final assessment is always made on a case-by-case basis. The use of general licenses must be reported to the BAFA no later than 30 days after export.
Whether and to what extent an export project is exempt from the permitting requirement depends on many conditions and is specific to each individual case. If you have any questions or uncertainties as to whether any of the exemptions listed here apply to your research/activity/project, please contact the export control officer.
Research security - Key questions:
With regard to research security (beyond the legal requirements of export control), researchers must develop a responsible awareness of the potential for misuse of their own work. In this context, research data, findings, ideas, samples, as well as specially developed software or prototypes, etc., not only have a particularly high scientific and thus social value, but may also be of interest to actors with non-scientific motives (financial, ideological, or political interests, pseudoscience, espionage, etc.).
A typical case study relating to research security is the use of geographical/political maps (country borders, geographical names) in publications:
In a jointly planned publication, the distribution area of an animal or plant species is to be presented in the form of a map. The cooperation, research work, methodology, and data related to the publication are completely exempt from approval with regard to export control regulations. Your international cooperation partners insist on using a different geographical overview map than your original map, which shows a different border of the country (than the one recognized by the UN). By accepting the proposal of your cooperation partners, you are not committing a criminal offense.
→BUT: By complying with this request, you may be legitimizing (also on behalf of the University of Greifswald) a state's potentially illegitimate territorial claims for political reasons. This could cause considerable damage to both your own reputation and that of the University of Greifswald. If no compromise can be found (e.g., omitting the map, using a geographical map without country borders, or using the originally planned map with a clear reference to the UN-recognized country border), you must not agree to the planned publication. (Regardless of this, many renowned academic journals also have clear standards for the use of maps.)
We are currently working on a comprehensive catalog containing information, behavioral guidelines, and further case studies as part of an internal compliance program. In this context, procedural and administrative processes are being adapted and these pages are being continuously expanded to provide you with the necessary and up-to-date information relating to research security and export control. To assess in advance whether your own research involves safety-related aspects in the sense of research safety or whether your research work is affected by export control regulations, please contact the export officer or the Committee for the Ethical Evaluation of Security-Relevant Research (KEF) at the University of Greifswald.
Case studies of security-related research
The development of the so-called Khan network is considered the best-known case of the transfer of knowledge and its misuse. After his education at European universities, Abdul Quadeer (A. Q.) Khan was able to become the “father
of the Pakistani nuclear bomb”. Through his proliferation network, he was able to pass on nuclear expertise and technology to other states such as Iran, North Korea and Libya, as well as to non-state actors.
Heupel, M. (2008): The A. Q. Khan Network. Transnational Proliferation Networks as a Challenge for International Non-Proliferation Policy, SWP Study, German Institute for International and Security Affairs; Berlin, https://www.swp-berlin.org/publications/products/studien/2008_S14_hpl_ks.pdf (in German only)
The Argo program can be cited as an example of scientific dependencies and uncertainties. The Argo programme, which has been collecting oceanographic data from the depths of the oceans since the early 2000s using free-drifting measuring buoys (known as Argo floats, of which around 4,000 are currently in operation) and transmitting it to data centres in the USA and France via satellites, is an example of scientific dependencies and uncertainties, even with regard to partners that have been classified as unbreakable to date. Germany is also participating in this programme with currently less than 7 % of the Argo floats, which are primarily deployed in the Atlantic. Overall, the USA provides more than half of all buoys (56 %, as of May 2025). This dependency poses major risks for modelling in climate research and current forecasting services, if access to the data is no longer guaranteed or the current network density is not maintained.
www.bsh.de/EN/TOPICS/Monitoring_systems/Argo_floats/argo_floats_node.html.
www.aoml.noaa.gov/two-decades-argo-program/.
globalocean.noaa.gov/research/argo-program/, https://argo.ucsd.edu
A study has identified five genetic changes that allow H5N1 influenza viruses, which are highly pathogenic to birds, to be transmitted between mammals via the air. These findings can help to better predict how such viruses could gradually develop into a threat to humans. This will make it possible to better assess the pandemic potential of pathogenic virus variants that regularly emerge in nature, gain insights for the early interruption of infection chains and, if necessary, develop targeted vaccines. There are risks associated with such Gain-of-Function-experiments on bird flu viruses, both in terms of unintentional pandemic outbreaks due to negligent behaviour in the laboratory, resulting in the viruses being released into the environment, and in terms of their misuse for the development of new biological weapons.
Herfst, S.; Linster, M.; Chutinimitkul, S. et al. (2012): Airborne transmission of influenza A/H5N1 virus between ferrets, in: Science, 336 (6088), S. 1534–1541, doi.org/10.1126/science.1213362, sowie Imai M.; Watanabe, T.; Hatta, M. et al. (2012): Experimental adaptation of an influenza H5 HA confers respiratory droplet transmission to a reassortant H5 HA/H1N1 virus in ferrets, in: Nature, 486 (7403), S. 420–428, https://doi.org/10.1038/nature10831.
A study investigates how young people consume extremist (Islamist) material on the internet and whether there is a link to radicalisation. The latter could be proven. It was found that it is not the depiction of violence that is relevant, but the intensity with which it is addressed. For example, video footage of beheadings is often viewed by young people. However, the potential for radicalisation is low. In contrast, only a few people visit online magazines of the so-called Islamic State or Al-Qaeda – albeit with a greater cognitive effect. Deradicalisation strategies can be developed on the basis of these findings. At the same time, however, they can help extremist and terrorist groups to improve their recruitment strategies. Studies of this kind can therefore both map out paths to de-radicalisation and provide a recruitment aid for terrorist groups.
Frissen, T. (2021): Internet, the great radicalizer? Exploring relationships between seeking for online extremist materials and cognitive radicalization in young adults, in: Computers in Human Behavior, 114, Artikel 106549
AI methods for detecting and eliminating software vulnerabilities
One example of this are AI methods for detecting and eliminating software vulnerabilities in the operating systems of Wi-Fi routers, smartphones and laptops. A research project has made it possible to develop automatic defence measures, but also to identify and exploit vulnerabilities in numerous devices that are not subject to regular checks and updates. For example, the “WannaLaugh” software package – as a counter-design to the malicious “WannaCry” – was developed to carry out and analyse ransomware attacks without causing any actual damage or spreading malicious software. However, this tool itself can also become a target and be misused like any other software. For example, the supposed malicious code could exploit vulnerabilities in WannaLaugh and carry out malicious actions so that it could ultimately be used for ransomware attacks.
Brundage, M.; Avin, S.; Clark, J. et al. (2018): The malicious use of artificial intelligence: forecasting, prevention, and mitigation, S. 25 f.
As example of a sensitive topic in medical research AI-supported systems for virtual toxicity testing of drug candidates with a view to drug development shall be referred to. Such systems are also able to identify particularly harmful molecules. With little effort, known toxins such as sarin or tabun can be detected within a few hours, as can previously largely unknown, highly toxic substances and those potentially used as arms. Even if further research is needed to stabilise such molecules and test their effect in the organism, the use of such software harbours risks with regard to the design of new types of chemical warfare agents.
Urbina, F.; Lentzos, F.; Invernizzi, C. et al. (2022). Dual use of artificial-intelligence-powered drug discovery, in: Nature Machine Intelligence, 4, S. 189–191, doi.org/10.1038/s42256-022-00465-9; Jakob, U.; Krämer, F.; Kraus, F. et al. (2024): Applying Ethics in the Handling of Dual Use Research: The Case of Germany, in: Research Ethics, 0(0), https://doi.org/10.1177/17470161241261044
An example of this is the planned visit of a foreign scientist from a country classified as critical, who wanted to participate in an electrical engineering project to optimise electricity, gas or water networks, in other words critical infrastructure, in Germany using AI methods. There is a risk of undesirable knowledge transfer in two respects: Firstly, the models on which the AI methods are based can be modified in such a way that they can damage or even paralyse the infrastructure instead of making the system more efficient. On the other hand, AI-based optimisation is based on detailed data sets, so that accessing them provides a comprehensive insight into the structural properties of the infrastructure. This exposes the structure and functional basis of the critical infrastructure in Germany and/or Europe and makes it (more) vulnerable.
One example of indirect cooperation is the case that came to light in January 2025, in which a German worked for a Chinese intelligence officer for several years (2017-2024) in order to gain knowledge about boat engines, sonar systems, aircraft protection systems, drives for armoured vehicles and drones for military use. Contacts were established with the research organisation via a company based in Germany. The university’s cooperation agreement was then concluded with the German-based company, which was, however, working with the Chinese secret service.
Generalbundesanwalt beim Bundesgerichtshof (2025): Anklage wegen mutmaßlicher geheimdienstlicher Agententätigkeit erhoben, 09.01.2025, https://www.generalbundesanwalt.de/SharedDocs/Presse-mitteilungen/DE/2025/Pressemitteilung-vom-09-01-2025.html.
An example of this is the request of a Chinese scientist who wanted to work on a research project on composite materials and manufacturing concepts on a TRL 3-5. The research project enables a reduction in mass by replacing metallic materials with polymer materials in carrier technologies such as aircraft construction. The employee visited the Nanjing University of Aeronautics and Astronautics (NUAA), which belongs to the Seven Sons of National Defence and is subordinate to the Ministry of Industry and Information Technology. If this request had been granted, there would have been cooperation with the Chinese military with a high degree of application proximity.
One example reports from Chinese students who record lectures at their host universities and report them to the authorities, for example when lecturers teach content that is “undesirable” from China’s point of view (e.g., referring to Taiwan as an independent country). Conversely, there are indications that the People’s Republic of China is exerting influence on academic institutions in the context of Confucius Institutes, which are also linked to higher education institutions in various ways. For example, there have been cancellations of virtual readings or attempts to prevent the tour of the documentary “In the name of Confucius” about the growing global controversy surrounding the work of the Confucius Institutes. This has led to press reports and further political activities and observations by the German domestic intelligence services (BfV).
Amnesty International (2024): Roundtable on Transnational Repression in the UK: lived experience and recommendations from Hong Kong diaspora community groups. A Summary Report, www.amnesty.org.uk/resources/roundtable-transnational-repression-uk-lived-experience-and-recommendations-hong-kong. Vgl. auch Deutsche Bundesregierung (Drucksache 20/14938, 10.02.2025): Antwort der Bundesregierung auf die Kleine Anfrage der Abgeordneten Peter Heidt, Gyde Jensen, Michael Georg Link (Heilbronn) und der Fraktion der FDP – Drucksache 20/14592 – Transnationale Repressionen durch die Regierung der Volksrepublik China in Deutschland, dip.bundestag.de/vorgang/transnationale-repressionen-durch-die-regierung-der-volksrepublik-china-in-deutschland/319579.
Ersteres betraf das Buch Aust, S.; Geiges, A. (2023): Xi Jinping. Der mächtigste Mann der Welt, 2. Aufl.; München, vgl. www.spiegel.de/panorama/bildung/chinas-einfluss-auf-deutsche-universitaeten-der-lange-arm-pekings-a-f6567e46-508f-4d64-a830-3816296dad79. Eine genauere Darstellung ist aus Gründen der Geheimhaltung nicht möglich. Vgl. hierzu auch Deutsche Bundesregierung (20.04.2022): Deutscher Bundestag 20. Wahlperiode. Antwort der Bundesregierung auf die Kleine Anfrage der Fraktion der CDU/CSU –Drucksache 20/1275 – Stand des Ausbaus der Asien- und China-Kompetenz im Wissenschaftssystem und Aktivitäten der Konfuzius-Institute in Deutschland, insbesondere S. 5, dip.bundestag.de/vorgang/stand-des-ausbaus-der-asien-und-china-kompetenz-im-wissenschaftssystem-und/286049.
For example, a visiting delegation was given the opportunity to gain insights into the equipment and methodology of an institution. Even if the research topic itself is not sensitive, the equipment could be of interest. It was observed that other foreign delegation members appeared unannounced and left the guided tour for some time. This allowed them to take pictures of the research department’s equipment and gain valuable information for other activities.
BfV (2022): Informationsblätter zum Wirtschaftsschutz. Spionage in Wissenschaft und Forschung; Berlin, S. 4, www.verfassungsschutz.de/SharedDocs/publikationen/DE/wirtschafts-wissenschaftsschutz/2023-01-17-infoblatt-spionage-in-wissenschaft-und-forschung.pdf.
Source protection is an example of an increasingly important ethical challenge when it comes to research projects in regions of the world from which people migrate to Europe legally or illegally. Not only migration issues are addressed here, but also questions of political dynamics in the region or other sensitive framework conditions. This means that confidential information or positions can be transmitted via the circle of people discussing this research together and be used for political purposes. Anonymising sources is both essential and difficult – especially in the case of well-known places and institutions that may be reported on in the media.
A German research institute wants to export parts with boron compounds and boron coatings to New Zealand.
Parts containing boron compounds and boron coatings are controlled by number 1C225 of Annex I to the EU Dual-Use Regulation. Their export is thus subject to authorisation pursuant to Art. 3 para. 1 of the EU Dual-Use Regulation.
For exports, a procedural facilitation in the form of a General Export Authorisation (GEA) may apply. In particular, GEA EU001 can be considered, which facilitates exports to the following countries outside the EU (known as EU001 countries): Australia, Japan, Canada, New Zealand, Norway, Switzerland (including Liechtenstein), the United Kingdom, and the United States.
A scientist plans to travel by plane to a third country. In his hand luggage, he wants to take a prototype covered by Annex I of the EU Dual-Use Regulation.
Variants:
a.) The item remains in the third country.
b.) The scientist takes the prototype back to Germany with him on his return journey.
c.) The prototype is not covered by any control list.
Re a.) The export is subject to authorisation pursuant to Art. 3 para. 1 EU Dual-Use Regulation. The manner in which the border crossing relevant for the export takes place is irrelevant for the existence of the authorisation requirement. The export can therefore also take place by being carried on the plane. Whether other security considerations prevent the prototype from being carried in hand luggage is not a question of foreign trade law.
Re b.) In this case, too, there is an export requiring authorisation pursuant to Art. 3 para. 1 EU Dual-Use Regulation. The fact that the export is only temporary does not affect the authorisation requirement. However, the temporary
nature of the export may have an impact on the project’s eligibility for authorisation.
Re c.) The export of an item may be subject to authorisation even if it is not covered by the relevant list of items. This is because an authorisation requirement can also follow from the so-called catch-all provisions. These can be found, among others, in Art. 4 of the EU Dual-Use Regulation and Section 9 AWV. According to these provisions, the export is subject to authorisation if the non-listed items to be exported are or may be intended, in their entirety or in part, for use in connection with NBC weapons or missiles suitable for this purpose (Art. 4 para. 1 lit. a of the EU Dual-Use Regulation), a military end-use in the country of arms embargo (Art. 4 para. 1 lit. b EU Dual-Use Regulation), or civilian nuclear facilities in Algeria, Iraq, Iran, Israel, Jordan, Libya, North Korea, Pakistan or Syria (Section 9 AWV).
A researcher flies to a third country and logs on to the intranet of his research institution with his laptop. The researcher has the option of accessing and, if necessary, working with technical documents from the research institution in Germany that require authorisation.
In this case, several facts regarding the permit requirements may be taken into account. The laptop, smartphone or USB stick may contain technology or software that requires authorisation. In this case, taking along the laptop and the technology or software stored on it already constitutes an export subject to authorisation.
Furthermore, an export in the form of “making available” the technology or software may be applicable, e.g. if the laptop can be used to access technology requiring authorisation, which is stored in the internal research network. Here, the possibility of accessing the technology is already enough. This means that there is an authorisation requirement even if the researcher does not access the technology subject to authorisation from abroad, but he has the possibility to do so.
A research vessel carrying listed dual-use items sets sail from the port of Hamburg and leaves the territorial waters, which extends over 12 nautical miles in Germany.
Variants:
a) The research vessel returns to the port of Hamburg without calling at any other port.
b) On its voyage, the research vessel calls at the port of a third country and then returns to the port of Hamburg.
If dual-use items are carried on a research vessel, an export is deemed to have taken place when the ship leaves the coastal area belonging to the territorial waters1 – regardless of whether it calls at the port of a third country. For an export to occur, it is sufficient that the customs territory of the EU has been left. It is not necessary for the items to cross the border to the national territory of a third country.
With regard to the individual variants, the following therefore applies:
Re a. and b.) Leaving the territorial waters of the state constitutes an export subject to authorisation pursuant to Art. 3 para. 1 EU Dual-Use Regulation.
A research institute wishes to send a satellite covered by number 9A004b of Annex I to the EU Dual-Use Regulation to a consignee in the USA for launching the satellite into Earth orbit from the Cape Canaveral Space Force Station (CCSFS). The signals from the satellite are then received by the research institute in Germany.
This is an export to the USA requiring authorisation pursuant to Art. 3 para. 1 EU Dual-Use Regulation. This also applies if the end-user of the satellite is an institution in Germany. The research institute can use the EU General Export Authorisation No. EU001 for the export.
A researcher from Germany is collaborating with a researcher from India to develop a new cultivation method for the Nipah virus. The German researcher sends his research results to the Indian researcher by email.
Human and animal pathogens, such as Nipah virus, may be covered by number 1C351 of Annex I of the EU Dual-Use Regulation. Technology under the General Technology Note for the development or production of equipment, materials or substances specified in 1C351 fall within number 1E001 of Annex I to the EU Dual-Use Regulation.
Hereafter: If the research results of the German researcher contain findings that fall under No. 1E001 of Annex I of the EU Dual-Use Regulation and if these are not already in the public domain or basic scientific research, the German researcher needs to apply for an authorisation to send the email to the researcher in India in accordance with Art. 3 para.1 of the EU Dual-Use Regulation. This is because the transmission of the email constitutes a border crossing into India.
Domestic research companies A and B, both established in the EU, pool their resources for a research project of research company C in a third country. In the course of the project, research company A asks research company B to send one of B's measuring instruments to the third country. The measuring instrument is listed in Annex I to the EU Dual-Use Regulation.
Variants:
- Research company A and B conclude a contract with C in which they jointly commit to the research project. A separate contract between A and B stipulates that A has the lead, which C is aware of.
- Research company A concludes the contract for the research project with C and is the sole contractual partner of C. In order to fulfil the contract, A involves research company B (effectively as a subcontractor).
- Research companies A and B each have contracts with C and take over the research project internally as equal partners. In the contract between B and C, B has undertaken to provide the measuring instrument.
The question arises as to whether A or B must apply for export authorisation. This depends on who is the exporter in the variants. This is largely determined by who is the dominant party in the project.
Re 1.) Although there is a contract between research company A and research company B with C, and B ships the measuring instrument, A has the lead, and so A controls the export transaction and is therefore the exporter.
Practice Tip: Since the exporter status is not at the disposal of the parties involved and internal agreements can therefore not influence the assessment of the exporter status, it is recommended to clearly regulate the responsibilities in the external relationship.
Re 2.) In this variant, A has the sole contractual relationship with C and B acts on A's instructions, effectively as a subcontractor. A is the exporter.
Re 3.) In this case, B has its own contract with C, has ultimate responsibility for the export and thus controls the export transaction. A does not have a lead. B is the exporter.
A professor publishes a research report. This can also be purchased in third countries after prior registration, which is open to anyone. In addition to general remarks, the report contains essential (necessary) technology for the development or production of dual-use items and thus falls under a list number of Annex I of the EU Dual-Use Regulation.
Variants:
a) The report containing listed technology is sent to a co-author or colleague in South Africa for review and comment before publication.
b) The professor would like to publish the research report in an American journal. The research report will also be accessible outside the USA after publication.
c) The professor sends the report to a publisher in Germany. The latter publishes the report worldwide.
d) Although the report contains technology, that technology is not necessary for the development or production of dual-use items and thus does not fall under any list number of Annex I of the EU Dual-Use Regulation.
The publication of listed technology constitutes an export or intra EU-transfer if the publication is also available abroad. Accordingly, an export or intra EU-transfer may also occur if the publication is by a German publisher. The decisive factor is whether the publication is also available abroad. If the publication is not available abroad, there is no export or intra EU-transfer subject to authorisation.
Hereafter: The publication of the research report constitutes an export subject to authorisation. Note: The application for an export authorisation must be submitted by the research institution or university employing the professor if the research report is to be published as part of the professor's professional activities.
Re a) If an article or a book containing controlled information (technology) is sent to a co-author or a colleague abroad for review and comment prior to publication, this also constitutes an export or transfer requiring authorisation according to the principles outlined above.
Re b) The EU General Export Authorisation No. EU001 cannot be used for export to the USA, as the professor knows that the research report will not remain in the country (USA) mentioned in EU001 to which it has been exported. Rather, the professor knows that the American publisher will make the research report available to a readership outside the USA. The professor must apply for an individual export authorisation. In principle, when working with publishers as part of the internal risk analysis, it is advisable as a scientist or research institution to obtain information on the countries in which the publisher will publish the research results that contain controlled dual-use technology.
Re c) It is questionable whether the exporter status belongs to the professor or her research institution or to the publisher. This always depends on the circumstances of the individual case.
If the publisher has committed itself to the professor to publish the research report worldwide and publishes the contents of the report unfiltered, it must be assumed that the professor is the exporter. The publisher would have a position comparable to that of a forwarding agent, so that the professor would have to submit the export application. The publisher takes over the actual act of publication (“crossing the border”) for the professor. However, it is she alone who decides on the export as such, as she alone decides to publish her research results via a publisher and thus to let the controlled technology out of her hands.
However, if the publisher independently reviews the content of the research report once again and, following this review, decides on the publication as such or has reserved the right to such a review and decision, this would speak in favour of the publisher having the status of an exporter. This would also be assumed if the publisher had influence on the amendment or omission of certain parts of the report.
The decisive factor is therefore who is responsible for the decision to publish, i.e. who bears responsibility for the publication in the internal relationship between the publisher and the author.
Re d) Since the technology is not listed, an end-use-related authorisation requirement within the meaning of the Catch-all provisions comes into question. In the case of application of Art. 4 para 1 lit. b EU Dual-Use Regulation, this requires the exporter's positive knowledge of a military end-use of the technology contained in the publication in an arms embargoed country. Even if worldwide publication by the exporter is suspected or considered likely, there is still no “positive knowledge” of use in an arms embargo country. As a rule, the professor (exporter) will not have any indications of a possible military end-use (exception e.g. publication in military journals, publication on a military item, the content of the technology relates exclusively to a military end-use).
As a general rule, when working with publishers and sharing publications that contain controlled dual-use technology, scientists should find out in which countries the publisher will be publishing the publication.
The EU is initiating a programme to create a globally accessible database of scientific data from EU-funded research institutions. Scientists from a German institute would like to put their data into this database.
Placing the data in the database constitutes an export subject to authorisation if the data is listed in one of the relevant lists of items and is neither already in the public domain nor part of basic scientific research. The fact that the database is based on an EU programme is irrelevant for the existence of the authorisation requirement.
a) A post-doctoral researcher from Pakistan would like to conduct a research project on radar systems at a German university.
Variants:
b) He is an Indian student.
c) An Iranian citizen with permanent residence in Australia would like to conduct research for his or her doctor thesis in the research field of valves and pumps at an institute in Germany. There are no indications for a sensitive end-use after the end of his or her research stay in Germany. He will stay in Germany for one year and has a visa from the German Embassy in Canberra.
Re a) This could be technical assistance requiring licence pursuant to Art. 8 para. 2 EU Dual-Use Regulation, Section 51 (1) AWV. The researcher is a foreigner who is not resident in an EU Member State or EU001 country (Art. 8 para. 3 EU Dual-Use Regulation, Section 51 (1) No. 2 AWV) and is temporarily present in the customs territory of the European Union. Accordingly, BAFA must be contacted if the researcher comes into contact with technology that can also be used, for example, for missiles of NBC weapons.
Re b) The information provided to a student will usually not be of the same quality as the information provided to a post-doctoral researcher. In the current constellation, it must therefore be carefully examined whether the information with which the student comes into contact is not in the public domain. If this is the case, no licensing is required (Art. 8 para. 3 lit. b Var. 1 EU Dual-Use Regulation, Section 51 (4) No. 1 AWV).
Re c) Based on Regulation (EU) No. 267/2012 (Iran Embargo Regulation) and the general provisions in Art. 8 EU Dual-Use Regulation, Sections 49 et seq. AWV, it must be checked whether technical assistance is prohibited or subject to authorisation.
Iran Embargo Regulation
In a first step, the prohibitions and authorisation requirements of the Iran Embargo Regulation must be examined. The prohibitions and authorisation requirements of the Iran Embargo Regulation require that the technical assistance (technical support) is provided to an Iranian person or for use in Iran.
The doctoral student is not an Iranian person within the meaning of the Iran Embargo Regulation. A natural person is to be viewed as an Iranian person if he or she has his or her place of residence or habitual abode in Iran (Art. 1 lit. o) of the Regulation). These requirements are not satisfied by the doctoral student who resides in Australia.
The condition for use in Iran could, for example, be met affirmed if the doctoral student intends to return to Iran in the near future; however, there are no indications of this in the present case. Technical assistance which is prohibited or subject to authorisation under the Iran Embargo Regulation is therefore not applicable.
Furthermore, there is no technical assistance subject to authorisation pursuant to Art. 8 in conjunction with Art. 2 No. 10 lit. c EU Dual-Use Regulation, Sections 49 AWV.
Since the doctoral student is conducting research at an institute in Germany, only the authorisation requirements set out in Art. 8 EU Dual-Use Regulation, Sections 51, 52 AWV may apply. However, an authorisation requirement according to these provisions is not applicable due to the lack of a context of end-use. With respect to Art. 8 of the EU Dual-Use Regulation and Section 51 AWV, it should also be noted that the doctoral student is not to be assigned to the group of addressees covered by Art. 8 of the EU Dual-Use Regulation and Section 51 AWV:
- Art. 8 in conjunction with Art. 2 No. 10 lit. c EU Dual-Use Regulation states that the addressee of the technical assistance is a person resident in a third country who is temporarily present in the customs territory of the European Union, with the exception of such persons who are resident in an EU001 country (Art. 8 (3) lit. a Var. 3 EU Dual-Use Regulation). These requirements are not met by the doctoral student who is resident in Australia, i.e. in an EU001 country.
- Section 51(1) AWV requires that the technical assistance is provided to a foreigner who is neither resident in an EU Member State nor in an EU001 country. These requirements are not met by the doctoral student who is resident in an EU001 country.
- Section 51(2) AWV only applies if the technical assistance is provided to a foreigner resident in an arms embargo country. This is also not the case with the doctoral student. Although he or she is a citizen of an arms embargo country (Iran), he or she is not a resident of that country. The doctoral student is resident in Australia.
a) You are planning to conduct a study in the field of brain research in connection with a foreign university. Research funds are available in this regard. You would like to leave the research funds to your partner university abroad to pay for the equipment or staff you need. Your check shows that the intended partner university is listed in Annex IX of Regulation (EU) 267/2012 (Iran Embargo Regulation).
Variant:
b) Instead of paying research money, you give high-speed cameras to the listed university. This is intended to generate income that the partner university can use to independently finance the research project.
Re a) Art. 23 para. III of the Iran Embargo Regulation stipulates that no funds or economic resources shall be made available, directly or indirectly, to or for the benefit of the natural or legal persons, entities or bodies listed in Annex VIII and IX. Accordingly, the payment of research funds is precluded by the prohibition on the provision of funds.
Re b) In addition to the provision of funds, Art. 23 para.III of the Iran Embargo Regulation prohibits the provision of economic resources. The term economic resource refers to assets of any kind that can be used to generate funds, goods or services. Thus, the transfer of the high-speed cameras instead of the transfer of funds is also prohibited. The purpose of the supplementary prohibition on making economic resources available (in addition to funds) is to prevent economic resources from being used as a parallel or substitute currency.
You supply a listed chemical to an unlisted university that wants to test the properties when mixed with other chemicals. The university works closely with a listed institute in this regard, as it has a specially equipped laboratory for this purpose. You are aware that in this context (part of) the listed chemicals are passed on to the listed institute. The supply to the unlisted university thus constitutes a prohibited indirect supply.
The export to the unlisted university therefore constitutes prohibited indirect provision. Based on your knowledge of this, the export fulfills the criminal offense of intent.
If you have no knowledge of a planned transfer by the partner university or could not reasonably have known about it (e.g., through publicly available information), the delivery to the partner university is not subject to permitting requirements.
B is an Indian citizen and has been residing primarily in Germany since 2015 (except for business trips, vacations, and visits to his home country) and has a residence permit based on previous employment. B initially studied in Germany and is now applying for a job at a university institute where he will have access to listed items.
It is to be assumed that B has his domicile and his habitual residence in the sense of a centre of life in Germany. If his residence permit is not limited to 5 years, B would be considered a national pursuant to Section 2 para. 5 in conjunction with para. 15 AWG. Section 51 AWV therefore does not apply.
Case studies by the Joint Committee on Security Related Research

